Working Anywhere: a winning formula for good work?
/The technology exists but for many individuals and organisations but it is not yet being used to its full potential.
Read MoreThe technology exists but for many individuals and organisations but it is not yet being used to its full potential.
Read MoreThere are thousands of education apps in the Windows marketplace, from early learning games to study aids and even apps that will help you manage the classroom, with more available every day.
Read MoreThis is a most interesting article from eWeek that summarises a lot that we in GDK experience on a regular basis.

Please call me or send me an emailif you wish to discuss your business and IT requirement further.
David O'Driscoll email: dod@gdk.ie
The research, which was commissioned by Epicor, surveyed more than 1,800 business leaders from 12 countries across the globe. The vast majority (89 percent) of organizations worldwide have experienced growth that hasn’t gone exactly according to plan, resulting in a significant level of anxiety among top business leaders about their company’s ability to succeed in the face of growth and change. The research, which was conducted by Morar Consulting and commissioned by Epicor, surveyed more than 1,800 business leaders from 12 countries across the globe.
Of those surveyed, 58 percent reported growth in 2015 and nearly 70 percent said they expect to grow in 2016, however only 11 percent experienced growth totally in line with their plans in 2015.
"The implications of an IT system that fails to scale are tremendous. Today’s IT systems are managing more than internal operations for a company," Celia Fleischaker, Epicor’s senior vice president of worldwide marketing, told eWEEK. "In many cases, IT systems are directly involved in managing interactions with customers. Survey respondents actually ranked the potential loss of customer intimacy or damage to the customer relationship as the No.1potential negative impact of growth."
Fleischaker said if IT systems can’t scale for growth, the pain the business will feel is significant and would potentially impact their customer relationships directly, in addition to putting stress on internal operations.
The top concern cited by CEOs was the perceived loss of customer intimacy that may come about as a result of growth.
Globally, significant levels of unplanned growth were more likely to be experienced by mid-sized businesses with 100-999 employees (37 percent), than larger enterprises with more than 1,000 employees (29 percent).
Growth was most likely to be described as painful (in as many as one in 10 cases) by smaller mid-sized businesses (100-249 staff) as they make the difficult transition from small to mid-sized enterprises.
To support business growth, and better prepare for its challenges, 79 percent of businesses believe that an effective and integrated IT infrastructure is essential.
The business leaders surveyed admitted they often fear the consequences of growth, citing a number of negative impacts when growth is not planned for effectively.
Around half (48 percent) said they worry that business growth puts excessive pressure on operations, damaging quality and customer satisfaction.
More than four in 10 (42 percent) said they were also concerned that their business IT systems may prove unable to cope with managing a larger, more complex, business model.
"In general, businesses need to look at solutions that provide them with an opportunity to better manage their touch points--with customers, with employees, and with suppliers," Fleischaker said. "Systems that support mobility and e-commerce while also providing support for their operations are critical. Selecting a cloud-based enterprise solution is also something to be considered as cloud can help reduce the complexity associated with an enterprise solution."

With the recent adverse weather conditions coupled with the impending Christmas Holidays, it is prudent to ensure that the offsite element of your Backup Systems is working efficiently. Please contact us if you have any concerns about your existing practices or if you want any further information regarding the GDK Hybrid Cloud Backup Solution.

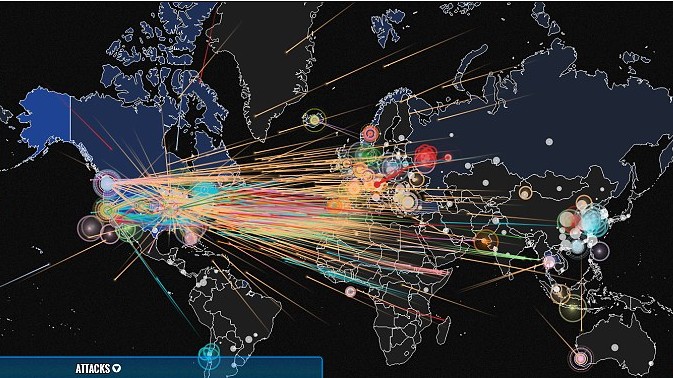
Cyber-criminals are constantly evolving their tactics. They employ several complex techniques to avoid detection as they sneak quietly into computer networks to steal valuable information.
How secure is your network? Explore the four primary strategies cyber-criminals employ to infiltrate your network and learn how to apply best practices and discover what your firewall needs to do to counter the cyber-attacks.
Counter-attack #1
Protect your network every minute of every day. Insist on a firewall that leverages the power of the cloud for real-time countermeasures to the latest malware threats. An effective firewall needs to be continuously updated, 24 hours a day, 7 days a week.
Cyber-attack strategy #1
Bombard networks with malware around the clock. Cyber-criminals work 24/7 to exploit your weaknesses especially out of date anti-malware technology.
Counter-attack #2
Ensure that your network is protected against all types of malware. To stay ahead of threats, consider multiple layers of protection against malware that provides continuous and timely updates to safeguard networks around the clock from millions of new malware variants as soon as they are discovered.
Cyber-attack strategy #2
Infect networks with different forms of malware. Cyber-criminals use different types of malware such as Viruses, Worms, Trojans, Spyware and Adware to catch you off guard. Trojans are designed specifically to extract sensitive data from the network.
Counter-attack #3
Choose a firewall that offers superior threat protection and high performance that has been independently tested and certified for network-based malware protection by ICSA Labs.
Cyber-attack strategy #3
Find and compromise the weakest networks. Cyber-criminals often target their victims based on the network weaknesses they discover
Counter-attack #4
Choose a firewall that protects against global threats. To block the latest global threats, invest in a security solution with global reach.
Cyber-attack strategy #4
Morph frequently and attack globally. New threats are popping up every hour on all continents.
Cyber-attacks are on the rise and firewall vulnerabilities are creating tangible business risks for your organization today.
GDK can assist you in a variety of ways to protect your computer systems:
1) Review the role of your Firewall:

2) Include GDK’s Web Protection as part of your Security Suite as well:
3) Implement GDK’s Email Security and Business Continuity Mail Solution as part of your configuration:

If you have any security concerns regarding Internet threats and protecting your business from Cyber Attacks please contact us and we can provide a free consultancy review. Ring us now or click here to Fill in the Contact Form.
We are here to assist you.
You can read more on the Cyber Attacks in this eBook
9 Reasons why Cloud Storage needs to be a part of your Business
Read MoreSince 1998, GDK Network Systems have specialized in the delivery of IT Technology solutions to Businesses and to the Education sector in Ireland.
With IT playing such a key role in business today, organizations partnering with the correct IT Solutions provider is a business-critical decision. Having a partner that you trust ensures that you get on with the day-to-day running of your operation while the IT infrastructure is left to your trusted IT partner. IT Managed Support services, Remote Support, Computer Supply, Citrix, Networking, Wireless, Promethean Reseller Ireland
Home IT Support IT Installation ©2017__GDK Network Systems Ltd. About Us Blog Contact Us